MSP Ransomware Protection Best Practices – CloudAlly
You are on the hackers’ hitlist. 4 out of 5 Managed Service Providers (MSPs) have been hit by ransomware last year, so much so that the US Secret Service issued a cybersecurity alert just for MSPs. ConnectWise’s 2022 MSP Threat Report underlined the particular rise of ransomware targeting MSPs, with it being responsible for 40% of the cyberattacks on MSPs. And it doesn’t look like it’s abating – there is a trend of a 10-15% increase in ransomware attacks on MSPs per quarter. As an MSP what steps can you take to protect your organization and your customers? In this guide, we share six tips on how MSPs can protect, detect and recover quickly from ransomware with minimal damage. By following these simple pointers, you can help keep your business – and your clients’ data – safe from harm.
1. What is Ransomware? How Does it Impact MSPs?
Ransomware is a type of malicious software (malware) used to encrypt data, locking users out of their files until a ransom demand is met. Many different types of ransomware exist, from locking or encrypting files to completely removing them or hijacking the system altogether. Due to ransomware’s ability to encrypt data and lock down systems, ransomware attacks can be especially harmful to businesses, and more so for MSPs as they are gateways to other organizations. The most common way that ransomware is distributed is through phishing emails, though it can also be spread through unsafe websites and file sharing.
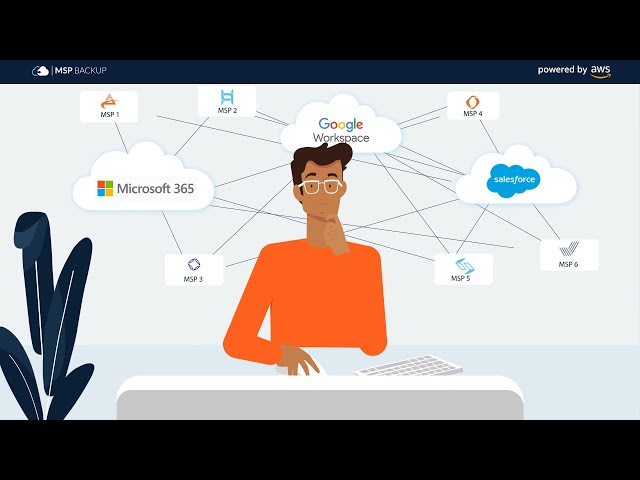
Managed Service Providers (MSPs) are attractive targets for ransomware attacks, as they are responsible for the IT infrastructure of multiple clients and thus the hackers can orchestrate a cascaded attack. As the spate of ransomware attacks on MSPs indicate, once hackers gain access to the server component of the MSP, they have a springboard to all of the MSP’s clients’ systems and data. For instance, the Kaseya MSP ransomware attack in turn impacted over 50 MSPs and between 800 and 1500 companies.
2. Keep your Software and OS Up-To-Date: MSP Ransomware Protection
Keeping your organization’s software and operating systems up to date is essential to prevent ransomware attacks on your MSP.
- Enable the auto-update feature wherever possible, but also ensure that patches are applied manually when auto-update fails or is not available. Make sure to periodically check that all of your software stacks are audit compliant.
- Monitoring of the IT infrastructure should be done daily, ensuring that only authorized software is being downloaded and used and software piracy or illegal software remain far away from your network environment.
- Email monitoring utilities, ransomware detection software, and firewalls with auto-updates should all be enabled and monitored regularly to stay secure.
- Furthermore, all firewalls, anti-virus software, and network monitoring tools should be switched on actively before updates are applied automatically to minimize disruption.
3. Encrypt your Data: MSP Ransomware Protection
Encryption is an effective way to prevent unauthorized access by abstracting private information and user credentials. Investing in high-quality encryption both at-rest (e.g. AES-256-bit encryption), and in-transit (e.g. SSL), is essential for companies to confidently secure their data. It is important that all the vendors processing your data use strong encryption methods as well. With these measures in place, organizations can protect their valuable data from malicious entities.
4. Use Strong Authentication: MSP Ransomware Protection
To gate-keep your apps and data from malicious cyberattacks, organizations should consider implementing a strong authentication policy.
- Firstly, enforce least-privilege access for all resources.
- For all SAML authentication using Okta is an excellent option to achieve this goal, as it provides single sign-on protection for users without the need for password resets or extra authentication steps.
- Further, enforcing Multi-Factor Authentication (MFA) or Two-Factor Authentication (2FA) for all user accounts ensures that unauthorized access can be prevented even if usernames and passwords fall into the wrong hands.
- OAuth should also be used to pass authorization between cloud applications, while there should be a robust mandatory password policy in place too.
- The overall goal is to prevent any unwarranted breaches of data security due to weak authentication strategies.
5. Train your Employees and Customers: MSP Ransomware Protection
Your employees can be the weakest or strongest defense against ransomware depending on how well-trained they are in cybersecurity. The importance of educating employees and customers on cybersecurity in the digital and work-from-home era cannot be understated. Especially as the main vector for ransomware is phishing emails – one wrong or right click can either cause or deflect a breach. I
- Investing in employee cybersecurity training helps ensure that vigilant and informed staff are aware of how to detect malware and ransomware red flags, avoid phishing clickbait, and notify admins of suspicious emails.
- Take a proactive approach by creating video tutorials and gamify cybersecurity with incentivized quizzes to encourage your customers and employees to participate.
- Regular updates should also be sent out periodically to their customer base in order to keep them abreast of the latest scams that could potentially cause harm.
- Finally, ensure that you have a robust and tested ransomware response plan (here’s a quick 5-step Ransomware Incident Response plan to get you started). It is important to outline clear communication and coordination with all relevant stakeholders – your support/legal teams and customers – throughout the incident response process.
6. Backup. But Make Sure It’s Secure: MSP Ransomware Protection
Security experts including the US Cybersecurity Agency recommend that “Backing up Is your best bet against ransomware”. When ransomware strikes, simply recover a clean copy from your backup, and drastically minimize the impact of the attack. However, ransomware attacks are increasingly aimed at essential data assets, such as databases and backups. If your backups are encrypted by the attackers, it’s as damaging as an attack on your production data. A few pointers to protect your backups from ransomware:
- Follow the 3-2-1- rule which is a best practice for ransomware recovery because it ensures that you have multiple copies of your data in different locations. Thus making it less likely that all copies will be lost or corrupted in the event of an attack.
- The backup application should be stringently encrypted and support secure authentication via Okta, 2FA, and Oauth.
- Ensure that the backups are immutable and air-gapped
- Check that your backup is GDPR and HIPAA compliant
- Test your backup and recovery processes and apps regularly
Recover ASAP from Ransomware with Backup for MSPs
Over 1000 Partners use CloudAlly Backup – a single solution that provides secure backup and smart recovery for Microsoft 365, Salesforce, Dropbox, Box, and Google Workspace. With unlimited AWS backup storage that is immutable, air-gapped, and secured with AES-256-bit encryption, CloudAlly ticks all the secure backup checkboxes. Recover ASAP from ransomware with unlimited point-in-time recovery. What’s more, we have a custom-tailored MSP Backup solution with a dedicated Partner Portal for unified customer management and a Learning Hub to help you quickly onboard your customers. Prefer to retain your own branding? Then simply use CloudAlly’s white-label cloud backup. All with zero-commitment licensing and pay-as-you-go pricing. Protect your MSP from ransomware no
Simplify MSP Backup with our Partner Portal. Watch How!