Let’s face it. Passwords are a bother – for the employee who has to keep thinking up a password every time it expires and for the Admin who’s struggling with securing the network and data against yet another brute force attack (there are 921 password spray attacks every second!). Except perhaps for the hacker in the corner who’s gleefully chuckling at the breaking into the organization’s network and systems thanks to a weak password. There is a knight in shining armor though and its name is Multi-Factor Authentication (MFA). MFA can block over 99.9 percent of account compromise attacks. It is “highly recommended” by Microsoft and is in fact a mandatory requirement for all of Microsoft’s Partners. In this blog we examine what is Multi Factor Authentication, why it is crucial to protect Microsoft Office 365, its benefits and how to set up Multi Factor Authentication in Microsoft Office 365.
What is MFA and Why is it Important in Microsoft Office 365?
Multi-Factor Authentication (MFA) or Two-Factor Authentication (TFA) is based on the concept of “Layered Security”. The layered security theory is about shielding your computer from various angles of attack and multi-factor authentication has been designed to assist you in that effort. MFA requires a user to enter two (or more) different factors in order to access their account. These factors could include a password, PIN code, biometric scan or one-time passcode that is sent through SMS or email. By increasing the number of steps before accessing an account, MFA makes sure no one can gain access without having a verification code or token at their disposal. Even if there were any security breaches, multi-factor authentication would ensure unauthorized individuals wouldn’t be able to take control of your account.
Microsoft Office 365 with its lucrative data is the prime target for hackers and is constantly assaulted with brute force attacks, credential thefts, phishing attacks, and account takeovers. Microsoft reported that there were “over 300 million fraudulent sign-in attempts to our cloud services every day.” Furthermore, the NIST reported that 54% of users use 5 or fewer passwords for all of their online accounts – so a compromised Microsoft 365 credential would probably mean that other apps, particularly those that authenticate via it would be compromised too. MFA helps to prevent credential theft and account takeover with its added layer of security for logging into Microsoft Office 365. It ensures that only the authorized person can access the account and offers comprehensive protection from cyber attacks, making MFA an invaluable tool within Microsoft Office 365.
Microsoft has gone a step further and added a requisite Office 365 MFA mandate for CSPs to be eligible for of their Partner Program. It states that, “all user accounts in the partner tenant must enable MFA to be able to“transact in the Cloud Solution Provider through Partner Center or via APIs”. A wise move as over 90 percent of accounts compromised by password attacks lacked strong multi-factor authentication (MFA), like SMS OTPs or FIDO2 authentication.
How Does Multi-Factor Authentication Work with Microsoft Office 365 Applications?
Multi-Factor Authentication (MFA) with Microsoft Office 365 provides extra layer of security to protect your accounts and data from unauthorized access. When enabled, you’ll be required to complete extra steps to verify your identity before logging in to Office 365. Typically, this means providing a one-time code sent to an authentication phone such as your office phone or via a mobile app.
How to Set Up MFA in Microsoft Office 365
Here are steps to set up Multi Factor Authentication in Microsoft Office 365. Easily add this extra protection for yourself and for others accessing Office 365 applications, a Global or Security Administrator can configure MFA settings via the Security & Compliance Center in the Microsoft Office 365 Admin center.
1. If you signed up for Microsoft 365 recently, MFA will already be set to “On” by default.
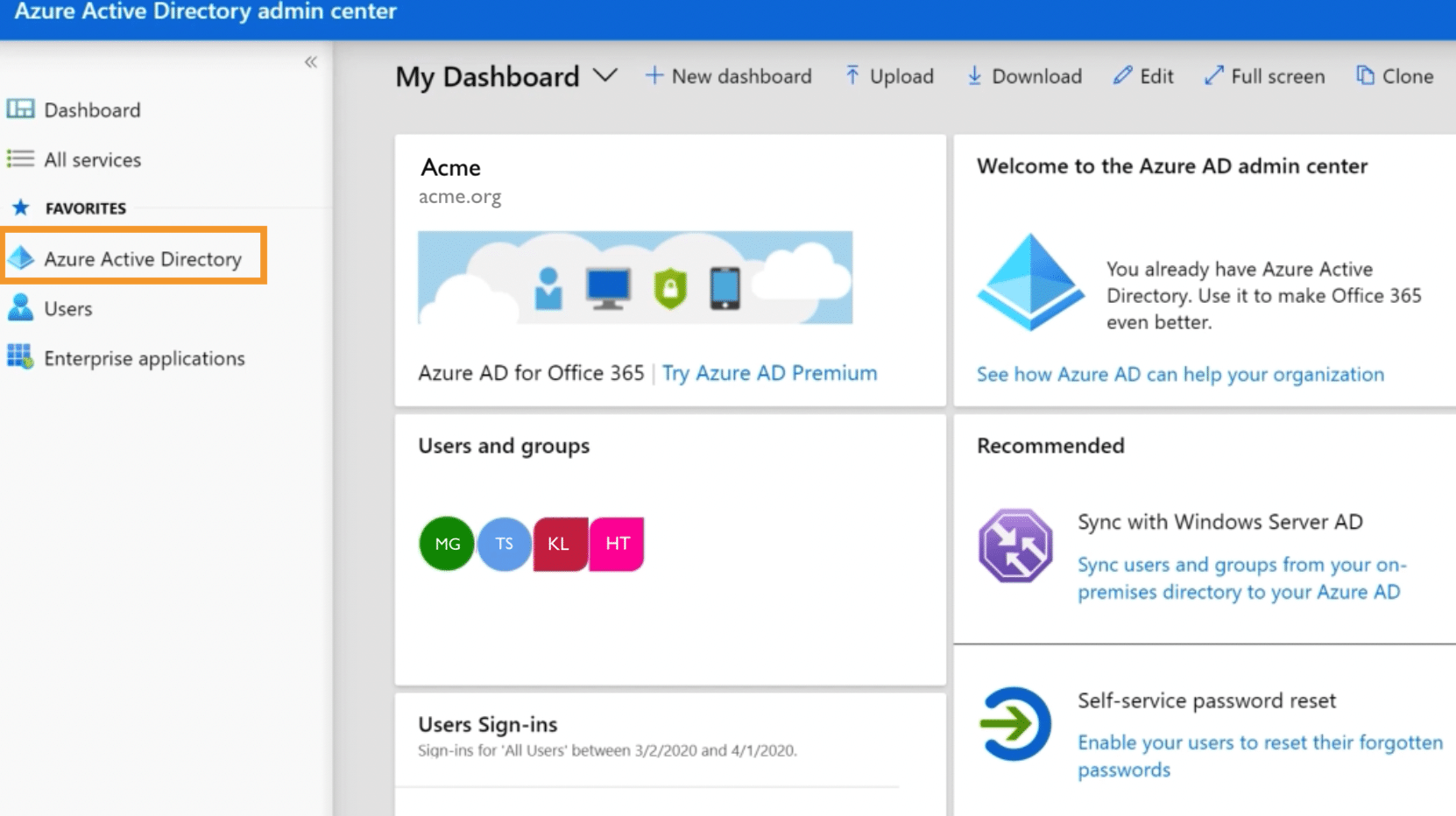
2. If not, or if you’d like to check the status, log in to the Microsoft 365 Admin Center, select Show All, and then choose the Azure Active Directory Admin Center. Then select Azure Active Directory
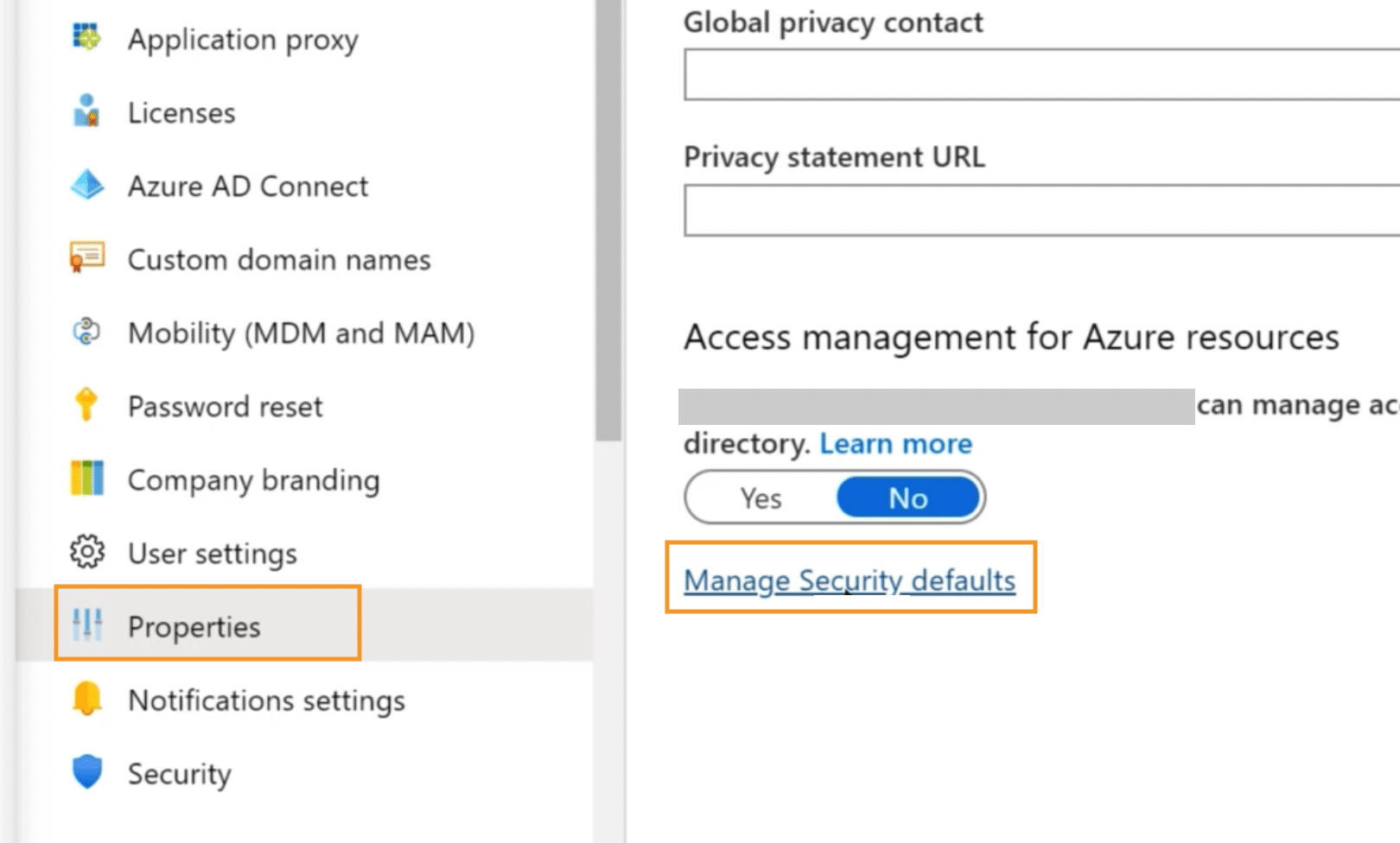
3. Select Properties from the menu on the left and then Manage Security Defaults
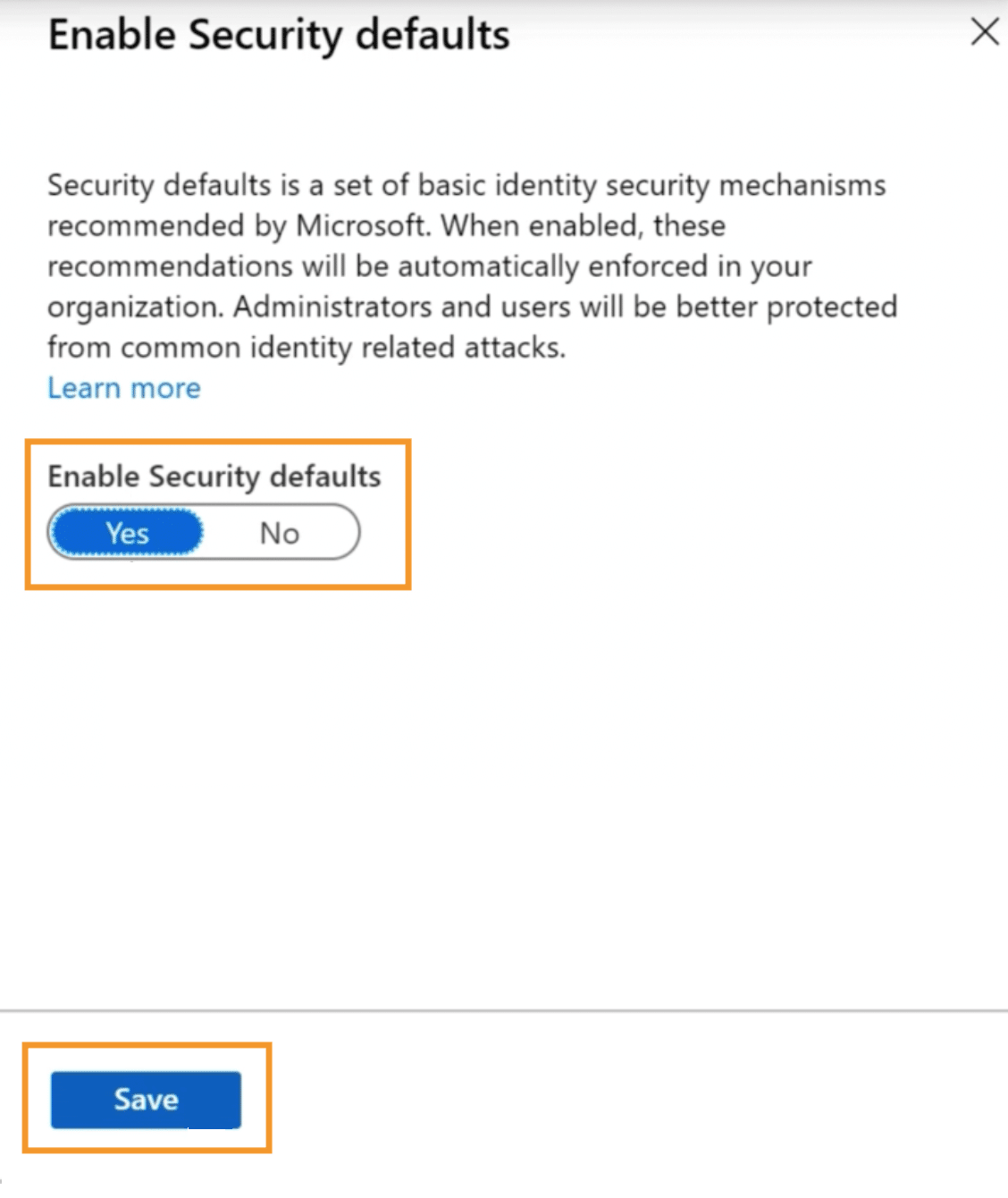
4. Under Enable Security Defaults select Next and finally Save.
5. The next time you or your employees login, you will be prompted to setup authentication on your mobile device.
Some points to note:
- If you have legacy per-user MFA turned on, turn off legacy per-user MFA.
- If you have Office 2013 clients on Windows devices, turn on Modern Authentication for Office 2013 clients.
- If you have third-party directory services with Active Directory Federation Services (AD FS), set up the Azure MFA Server.
- You can also explore enabling passwordless authentication using the Microsoft Authenticator app to sign into any Azure account
What Are the Benefits of Multi-Factor Authentication in Microsoft Office 365?
Multi-factor authentication in Microsoft Office 365 has undeniable benefits to secure your data from unauthorized access and credential theft.
- Stronger password security: While passwords remain one of the most frequent ways of identification, two-step verification provides stronger security by combining existing methods such as personal emails and text messages for a more secure option.
- Enhanced monitoring: Establishing multi-factor authentication on Office 365 allows IT admins to monitor system locations and activities, stopping any malicious attempts instantly for greater security.
- Prevents account takeover: MFA also helps to prevent against account takeover through reliable detection of unauthorized activities or suspicious logins from untrusted locations allowing monitored permission control within the administrative systems.
- Ensure compliance: Microsoft strongly recommends MFA and mandatorily requires it to be enabled for all its third-party partners. Regulatory laws too require you to implement best practices for secure authentication.
- Recommended by experts, Trusted by customers: Using MFA or 2FA is one of the top three things that security experts do to protect their security online, according to a recent Google survey. Your customers concur – almost 9 in 10 (86%) say that using 2FA makes them feel like their online information is more secure, according to TeleSign.
In short, multi-factor authentication is a simple yet powerful step to ensure stronger security in Microsoft Office 365.
Secure Your Microsoft Office 365 Data with MFA-Compliant Backup
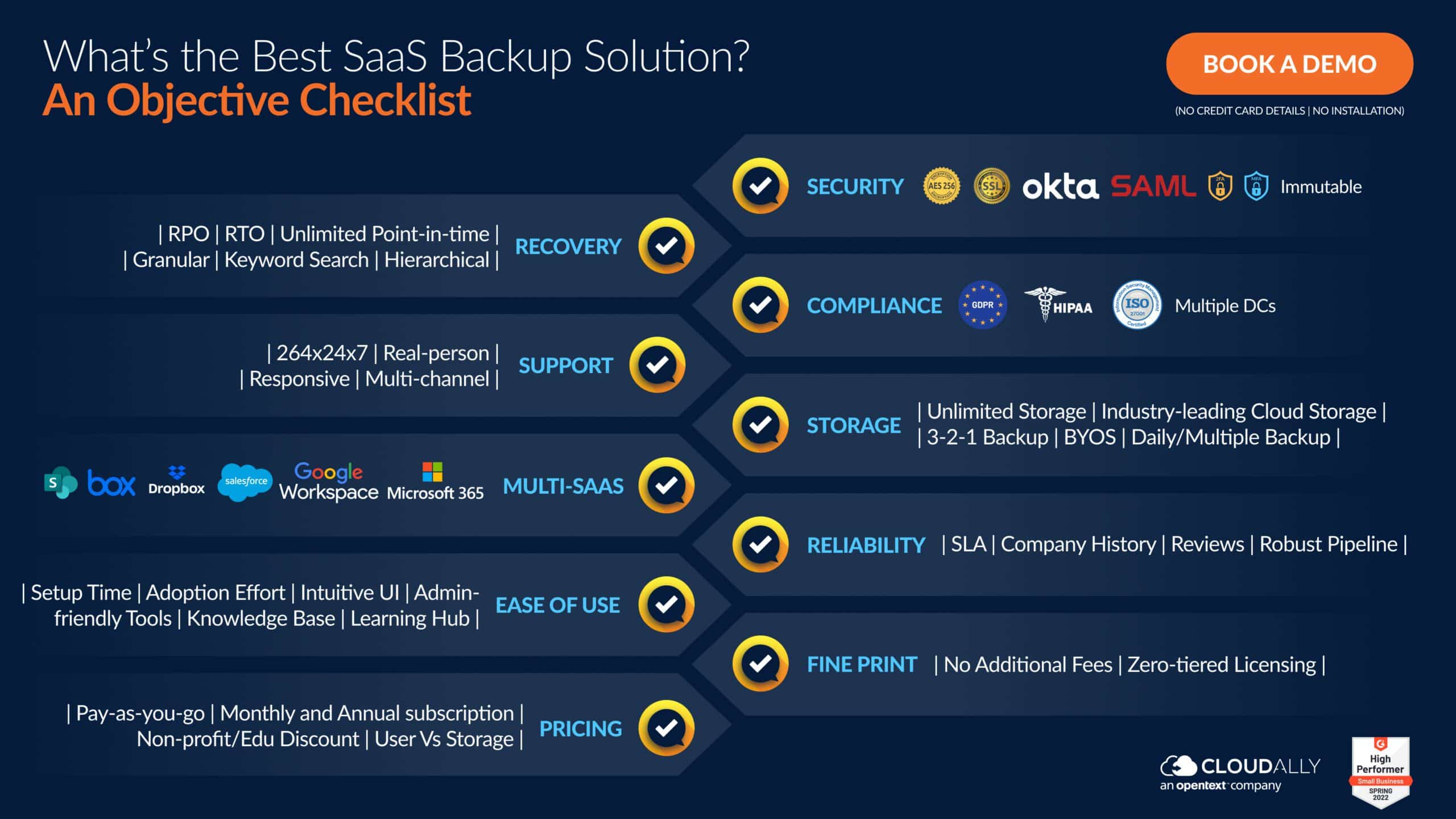
We’ve detailed above how Multi-Factor Authentication is an important best practice for organizations in order to secure their Office 365 environment. The best way to protect your organization’s data is not only by setting up MFA for your organization, but making sure that all your third-party vendors have MFA set up too. As we’ve seen with the spate of supply chain attacks, a breach of any of your vendors that have access to your network and data, is a breach of your organization too. Moreso for your backup vendor who has access to all your valuable Microsoft Office 365 data. Do they have an option to enforce MFA? Below if an objective checklist to ensure that your Backup provider ticks all the checkboxes, particularly as far as Security and Compliance go.
CloudAlly Backup for Microsoft 365 comprehensively protects Mail, Calendar, Contacts, Tasks, Teams, OneDrive, and SharePoint with secure backup on AWS S3 storage and smart recovery from any point-in-time and level of granularity (just type in a keyword and we’ll find the file/email).
Start a Free Trial (No Commitments | No Payment Details | Unlimited AWS Backup) or Book a Demo now!