Essential Reads on Ransomware: Protection, Recovery, and Insights
It’s that time of the year again for “Best/Worst of 2022” lists. We usually do an annual round-up of our top Data Protection blogs, but this year they all belong to one category – Ransomware. No surprise, considering that Ransomware has hogged the limelight in 2022. Ransomware reinvented itself as a successful business venture with LockBit 3.0’s lucrative “Ransomware-as-a-Service” (RaaS). Its ingenuity was further expanded with the Royal and Cuba strains of non-affiliate, multi-threaded ransomware which are “amassing as many victims as they can before the holidays, in preparation for 2023”. Reports say organizations could be under attack by ransomware every 2 seconds going forward, from every 11 seconds in 2022. Better buckle up for a wild ride! Here are five of our top Ransomware blogs in 2022 with proven real-world pointers to detect, protect, and recover from ransomware in 2023.
Top Ransomware Blogs of 2022
#5 Know Thy Enemy: Understanding the Brutal Cost of a Ransomware Attack
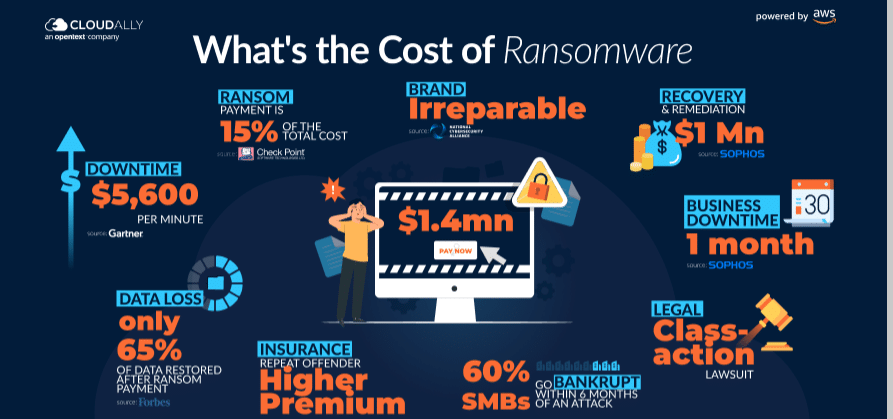
The first step to vanquishing your enemy is understanding it. In this blog, we examine the true cost of a Ransomware attack. Surprisingly, the ransom only accounts for 15% of the cost of ransomware. The bulk of the cost is expended due to downtime, data recovery, and remediation. Here is an infographic to put it into perspective.
#4 Preparation is Your Best Bet: How to Create a Ransomware Incident Response Plan
A robust and viable Ransomware Incident Response Plan is your best bet for recovering from ransomware with minimal impact to downtime and business continuity. In this blog, we list 5 steps to creating such a plan starting with attack validation, communication protocols, containing the attack, ways to recover your data from ransomware, and finally how to retrospect and continually improve the plan.

#3 Spotlight on Solutions: Ransomware Protection and Recovery in Microsoft Office 365 and Microsoft SharePoint
We next provide solution-specific pointers with our blogs on SharePoint Ransomware Recovery and Ransomware Protection with Microsoft Office 365. Microsoft Office 365 and SharePoint have been the most-targeted SaaS platforms. Explore native and third-party options for Microsoft (Office) 365 ransomware protection as well as ways to recover your SharePoint data after a ransomware attack.
Watch the video below to hear how a leading MSP recovered from a SharePoint ransomware attack (on Christmas Eve!)
#2 Spotlight on Industries: Ransomware Protection for SMBs and Healthcare
Ransomware has indiscriminately targeted all industries, but its pet targets have been SMBs and the healthcare vertical. Here are 5 strategies for SMB Ransomware Protection for small and medium businesses to identify, protect, detect, respond to, and recover from ransomware. We then turn the focus on the beleaguered healthcare industry which has proven to be a lucrative target for ransomware with its valuable ePHI. Our blog provides four remedies for ransomware attacks on healthcare including ways to secure applications and endpoints, improve detection capabilities, restrict access to data and systems, and invest in post-ransomware recovery.
Watch the video below to see ransomware data recovery in action
#1 Finally, the Hidden Loophole: Protecting Backups from Ransomware
Your data is only as safe as its backup. Hackers are increasingly targeting backups as a backdoor entrance to an organization’s data and systems. Our blog, How to Protect Backups from Ransomware details 5 tips to secure your backups including cyber-resiliency, strong encryption, secure authentication, employee cybersecurity training, and regular testing of backups.
We hope you benefited from the pointers above. Stay tuned for more insightful content on Ransomware by subscribing to our blog.




