What’s keeping our army generals up at night? Likely, a phishing attack. In our digitalized world, cyber attacks are consistently the weapon of choice bringing down companies (the cost of a breach is a debilitating $3.86 million) and F-35 fighter jets (more likely than a missile would). Malware attacks are surging higher- cybercrime was up 600% due to the COVID-19 pandemic. What’s worrisome though, is that we’re unprepared – 78% lack confidence in their company’s cybersecurity posture. As we celebrate Cybersecurity month, let’s walk through the essential aspects of a robust cybersecurity plan – your lifesaver when an attack strikes. We will especially analyze how backups are a part of a cybersecurity plan. It is a part of the five elements of the NIST cybersecurity framework, the leading cybersecurity plan, as the only reliable way to reverse or mitigate the damage of a cyber attack.
Are Backups a Part of a Cybersecurity Plan?
- The 5 Elements of the NIST Cybersecurity Framework
- Where does Backup Fit in the Cybersecurity Plan?
- What Value Does Backup Bring to Your Business?
Analyzing the Gold-Standard: The NIST Cybersecurity Framework
A cybersecurity plan helps an organization to protect and defend itself from cyber attacks and mitigate its risks. A hardy cybersecurity plan needs to be versatile, dynamic, and have a broad set of strategies, policies, and technologies that have not just one but many components. Let us go over the five aspects of the industry’s gold standard in cybersecurity planning – The National Institute of Standards and Technology (NIST) cybersecurity framework
The Five Elements of the NIST Cybersecurity Framework
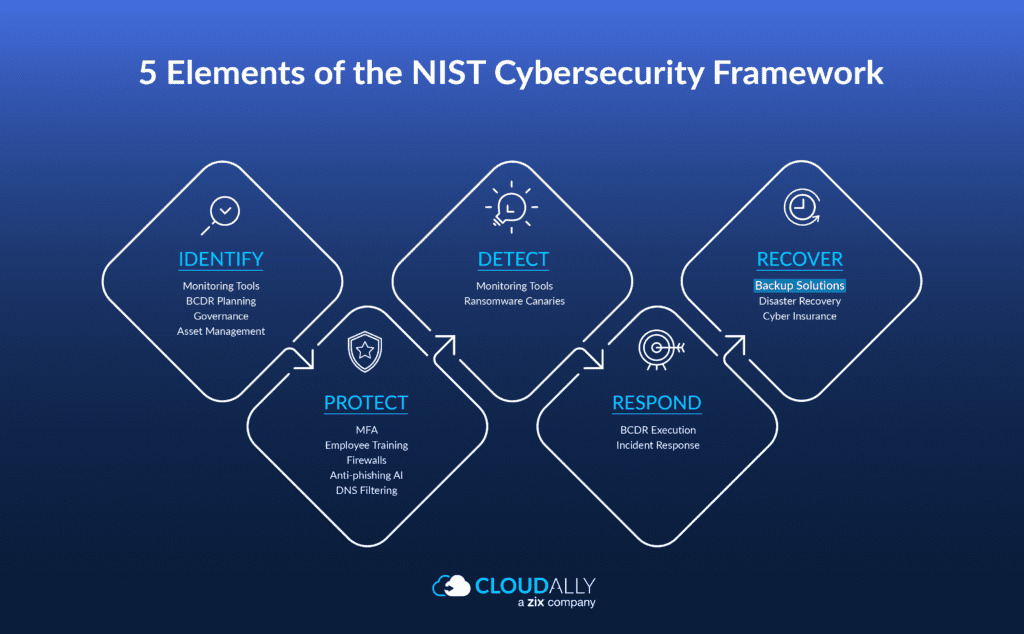
#1 Identify: NIST Cybersecurity Framework
Understand and identify the cybersecurity business impact and touchpoints across infrastructure, employees, and data.
Deliverables: List of physical and software assets, Asset vulnerabilities, Regulatory requirements, Cybersecurity policies, Risk Management Strategy, Supply Chain Risk Management strategy
Tools: Monitoring Tools, BCDR Planning, Governance, Asset Management
#2 Protect: NIST Cybersecurity Framework
Outline the safeguards and framework to put in place to secure your infrastructure and data such as to mitigate the risks.
Deliverables: Data Protection and Privacy policies, Identity management and access control best practices, Setup of the office of Data Protection, Employee Cybersecurity Training, BCDR Planning
Tools: MFA, Firewalls, Anti-phishing AI, DNS Filtering
#3 Detect: NIST Cybersecurity Framework
Framework for a timely detection of a cybersecurity breach.
Deliverables: Continuous monitoring framework, impact assessment.
Tools: Monitoring tools, ransomware canaries
#4 Respond: NIST Cybersecurity Framework
Processes to ensure appropriate and audit-compliant responses to a breach.
Deliverables: Response plan, Breach response reporting process for law enforcement and regulatory authorities, communication processes for management, employees, and customers, Setup of an Incident Response team.
Tools: BCDR execution, Incident Response mechanisms
#5 Recover: NIST Cybersecurity Framework
Activities to ensure data resilience, disaster recovery, and business continuity in the aftermath of a cybersecurity incident.
Deliverables: Review and improvement of existing plans and policies namely the BCDR plan.
Tools: Backup Solutions, Disaster Recovery, Cyber Insurance
Where does Backup Fit in the Cybersecurity Plan?
“Businesses need to ensure they have a trusted backup of their key systems and have tested and practiced recovery plan from if those systems were compromised”
David Cripps, the CISO (Chief Information Security Officer),
Are backups a part of a cybersecurity plan? Well, it’s one of the most important components of a strong cybersecurity plan that is often missed out – resilient and fast backup and restore. In the NIST cybersecurity framework discussed above, backups are a part of the “Recover” phase. Crucially, backups are an important constituent of a robust Business Continuity and Disaster Recovery plan (BCDR) which spans multiple phases of the cybersecurity framework. Although the NIST Cybersecurity framework has many phases to prevent successful cyberattacks, the attack vectors are constantly changing and the plan must take into account that some attacks might succeed. That is when restoring from a cloud backup becomes the best solution to mitigate the damage and ensure business continuity.
This is even more true today with the increasing ransomware storms buoyed on by security vulnerabilities of the remote workforce and the en masse digitization due to the pandemic. When adopting cloud platforms like SaaS platforms such as Microsoft 365, Google Workspace, and Salesforce Backup, note that the Shared Responsibility Model puts the onus of data protection on you, as the data controller. Secure backup and recovery is the only way to vaccinate your data against the cyber pandemic. You need to perform both daily backups of the SaaS applications and have the ability to restore files, mailboxes, folders, and sites in a quick and simple manner. One without the other means the effort is incomplete. It is just as important to regularly conduct end-to-end backup and recovery testing so that you can be sure that when a restore is needed due to a cyber-attack, the recovery will work.
What Value Does Backup Bring to Your Business?
The value and advantages that backup brings to your business and your organization’s cybersecurity is three-fold:
#1 Advantage of Backup for Business: Better Cybersecurity Due to Data Recoverability from any Point-in-time
Backups are a fundamental part of the “Recover” phase of your cybersecurity plan. As Gartner puts it, “Organizations that assume SaaS applications don’t require backup, or that the SaaS vendor’s data protection Is good enough, may place critical data at risk”. Native options do not offer unlimited point-in-time or granular recovery. This feature is a must for any organization, given that the average time to detect a breach is 180 days, well after the time-bound limits of native recovery. Stay cybersecure with unlimited point-in-time data recoverability.
#2 Advantage of Backup for Business: Regulatory Compliance With Assured Recoverability
Regulatory laws such as GDPR, HIPAA, CCPA, and others require data controllers to have demonstrable recoverability. GDPR’s Article 32 mandates that companies “have the ability to restore the availability and access to personal data in a timely manner in the event of a physical or technical incident”. Stay audit-compliant with secure backup.
#3 Advantage of Backup for Business: Increased Productivity Due to Optimal Business Continuity
Optimal Recovery Point Objective (RPO) and Recovery Time Objective (RTO) facilitate optimal business continuity. Automated daily SaaS backup ensures that your backup holds a recent accurate copy of data for an optimal RPO. One-click quick recovery similarly ensures that you have an optimal RTO. Stay productive with reduced downtime and seamless business continuity.
Experience for yourself the value-add that secure SaaS backup brings to your organization’s cybersecurity. Try a free, full-feature trial of CloudAlly Backup for Microsoft 365, Google Workspace, Salesforce, Box.com, and Dropbox. Are you an MSP, CSP , or VAR? Try our tailored MSP Backup or white-label OEM backup with a dedicated Partner Portal. Zero commitment, zero setup, zero fine print – full ROI.