Security experts all agree. The best way to recover from malware and ransomware is to have a robust backup and recovery plan in place. The Cybersecurity and Infrastructure Security Agency (CISA) emphasizes, “Backups are critical in ransomware recovery and response; if you are infected, a backup may be the best way to recover your critical data”. However, security vulnerabilities of backups offer a lucrative opportunity for hackers. There are increasing incidents of backups being explicitly targeted by malware. Once the backup is compromised, hackers gain an entry point into your network, obtain easy access to all your data, and infect the one reliable recovery option – your data backup. So how do you secure your backups? We detail best practices including ways to secure backup authentication with SAML (Okta) and MFA/2FA.
Why is it Important to Secure your Backup?
Your backups are only as secure as the authentication methods you use to protect them. If your backups are not properly secured, they could be accessed and tampered with by unauthorized individuals. Examples of a data breach due to compromised backups can include the following:
- A hacker gains access to your backup server and copies all of your data
- An employee with access to your backup server copies or deletes sensitive data
- A virus or malware infection on your backup server destroys or corrupts your data
To protect your data from these and other potential threats, it is important to use secure authentication methods such as SAML and MFA/2FA.
Secure Backup Authentication with SAML and MFA/2FA
How does SAML (Okta) Secure Your Backup Authentication?
Credential theft is the leading cause of data breaches. The risk is multiplied when employees have to log in with different credentials for multiple apps. SAML (Security Assertion Markup Language) mitigates the risk with secure Single Sign-On (SSO). It is an open standard that allows service providers to communicate authorization credentials from identity providers (IdPs) to applications. Quite simply, SAML allows secure interaction between apps and enables users to access all their applications with a single set of credentials.
SAML protects your backups from being breached in the following ways:
- Secure Transmission of Backup Credentials: SAML binds the user’s identity to a security token issued by a recognized vendor, which then transmits the user’s personal information to service providers. This ensures that only the direct credentials of your backup are sent, reducing the risk of phishing or identity theft. Thus helping to prevent unauthorized access to your backup data and reducing the risk of data breaches.
- Mitigate credential theft: Employees only need to remember one username and password combination across all the SAML-enabled applications. These credentials are the same as the ones used for SSO, so employees do not need to create or maintain multiple passwords. This reduces the risk of credential theft due to weak passwords and stored credentials.
- Other nice-to-haves:
- Improve UX: Can’t beat the elegant simplicity of SSO for employees.
- Simplify user management: Additionally, IT admins skip the hassle of managing employee access rights for multiple applications. With SAML each user can be managed from a single directory.
- Reduce costs: By reducing the number of credentials and ensuing ticket submissions and password resets, SAML brings down admin effort. As it is an out-of-the-box solution for authentication, you save the development costs often associated with proprietary authentication methods.
CloudAlly Backup provides secure backup authentication with SAML with Okta integration. Watch how to securely authenticate your backups via Okta
Secure Backup Authentication with SAML via Okta
How does MFA/TFA Secure Backup Authentication?
You may have an extremely strong password policy. However, know that most typical malware assaults, such as phishing, credential stuffing, and keystroke logging, can easily break through the strongest password policy. Hackers employ credential interception, database hacks, and/or network scanning to steal the actual password, making its apparent “strength” irrelevant.
MFA (Multi-Factor Authentication) / 2FA (Two-Factor Authentication) adds an additional layer of security by requiring users to provide two or more factors of authentication, such as a password and a security code from a mobile device. It has been demonstrated that MFA’s multi-layered security has allowed it to successfully block 99.9 percent of data breaches due to compromised credentials. So much so that Microsoft has mandated MFA for all its Cloud Solution Provider (CSP) program partners.
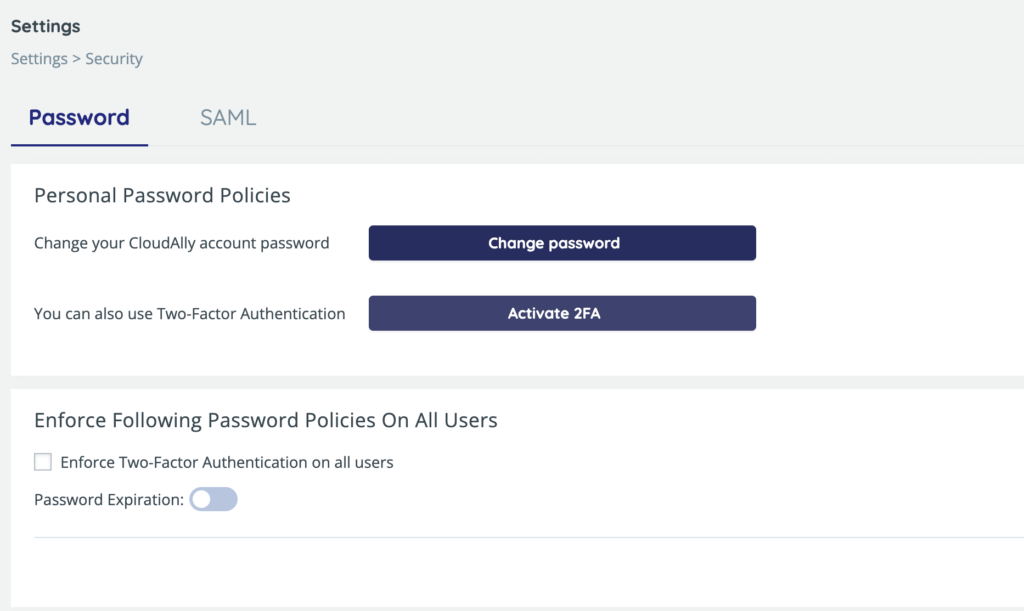
If your backup requires MFA, the user will have to provide both a password and (typically) a security code from a mobile device. Adding that additional layer of security helps to prevent unauthorized access to your backup data. CloudAlly Backup allws you to enforce 2FA and password expiration, thus providing stringent backup authentication.
Secure Backup Authentication with Mandatory TFA and Password Expiration
Stringently Secure Backup With CloudAlly
CloudAlly backup supports SAML authentication via the leading industry provider Okta in addition to OAuth for secure authentication. In addition, CloudAlly also supports MFA with an option to enforce it across your organization. This means that you can secure your backup data with the same strong authentication methods that you use to protect other sensitive data in your organization. Thus protecting your backup from credential theft and infiltration. Apart from secure backup authentication with SAML (Okta) and MFA/2FA, CloudAlly offers best-in-class application security with backups stored on Amazon Web Services (AWS) S3 storage, intrusion detection, and AES-256 bit data encryption at-rest and in-transit. CloudAlly is also audit-ready with ISO 27001 certification, HIPAA/GDPR compliance, and the option to choose from six data centers worldwide. Read more about our backup security credentials.
Get end-to-end protection of all your SaaS data – Microsoft 365, Google Workspace, Salesforce, Dropbox, and Box with CloudAlly.
Start a Free 14-day Trial (5-min setup (honest!) | No credit card | All Features Included)